Userpilot is now SOC 2 Type II Certified! Learn About Our Information Security Standards

SOC 2 Type II is one of the highest information security standards available for SaaS companies. At Userpilot, we know how essential information security is for your company. That’s why Userpilot has subjected itself to a stringent data security audit by an independent auditor. In order to ensure our information security measures are of the highest standard – we have been audited by Barr Advisory, and awarded the SOC 2 Type II certificate.
Userpilot is a product growth platform that allows you to analyze your users’ behavior inside your product, create personalized in-app experiences for them to improve their product experience, as well as collecting their sentiment and opinions via NPS and microsurveys. Needless to say – we process a lot of user data and take the matters of data security extremely seriously.
Let’s look into what SOC 2 Type II is, why it’s important, and what Userpilot’s new certification means for your company.
Summary
- SOC 2 is an auditing procedure by AICPA ensuring the security of client data processing by 3rd party service providers.
- SOC 2 certification is based on the service providers meeting the 5 “trust service principles”: security, availability, processing integrity, confidentiality, and privacy
- SOC 2 audit involves visits from the auditing body to the audited company and observing its systems and their effectiveness in a controlled environment for a period of 3-9 months, to check how the company’s systems meet the 5 service trust principles.
- SOC 2 Type I assesses only the description of the company’s systems. SOC 2 Type II additionally evaluates its operational efficiency.
- Userpilot’s SOC 2 audit was conducted by Barr Advisory, trusted cloud-based security, and compliance advisory body.
- The benefits of choosing SOC 2 Type II certified service providers like Userpilot include: data breach prevention, lawsuit, and bankruptcy protection, increased credibility and trustworthiness, and a higher chance of closing enterprise deals.
- Current and future customers of Userpilot can now be sure about its date protection mechanisms quality and can learn all the details from the SOC 2 report, available upon request.
What is SOC 2
SOC 2 is an auditing procedure developed by the American Institute of CPAs (AICPA), which ensures the security of your data processing by third-party service providers such as SaaS and cloud companies.
SOC 2 defines criteria for how service providers should manage the data of their customers.
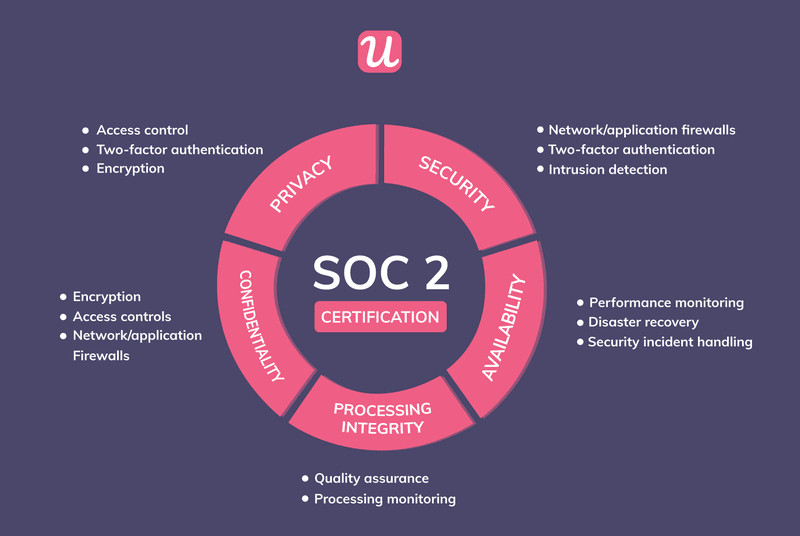
The criteria are based on five “trust service principles”:
- security
- availability
- processing integrity
- confidentiality
- privacy
Each organization has to design its own control procedures to ensure compliance with one or more of the SOC2 trust principles – so the SOC2 reports will be different for every organization.
The reports cover information about how the service provider manages the data of their clients/customers. SOC2 audits and reports are conducted by independent advisory bodies.
SOC 2 audit process
The auditing body visits the audited company and observes its systems and their effectiveness in a controlled environment for a period of 3-9 months. This includes on-site meetings, discussions with the management responsible for the respective systems who need to present detailed descriptions of their systems and controls, as well as a lengthy evaluation process with lots of questions.
The examination of the description of the system and the suitability of the design and operating effectiveness of controls involves the following:
- Obtaining an understanding of the system, commitments and service requirements
- Assessing the risks that the description is not presented in accordance with the description criteria and that controls were not suitably designed or did not operate effectively
- Performing procedures to obtain evidence about whether the description is presented in accordance with the description criteria;
- Performing procedures to obtain evidence about whether controls stated in the description were suitably designed to provide reasonable assurance that the service organization achieved its service commitments and system requirements based on the applicable trust services criteria;
- Testing the operating effectiveness of controls stated in the description to provide reasonable assurance that the service organization achieved its service commitments and system requirements based on the applicable trust services criteria; and,
- Evaluating the overall presentation of the description.
The aim of the SOC 2 audit is to answer the following questions about the systems in the subjected company in regard to the 5 “trust principles”:
Security
- Is the system protected against unauthorized access (both physical and logical)?
Availability
- Is the system available for operation and use as committed or agreed (e.g. by an SLA)?
Processing Integrity
- Does the system achieve its purpose (i.e., delivers the right data at the right price at the right time)?
- Is the data processing complete, valid, accurate, timely, and authorized?
Confidentiality
- Is the information designated as confidential protected as committed or agreed?
- Is access to and disclosure of confidential information restricted to specified people or organizations?
- Are appropriate measures such as network and application firewalls in place to protect data confidentiality?
Privacy
- Do the system’s collection, use, retention, disclosure, and disposal of personal information conform with the organization’s privacy policy?
- Does it conform with AICPA’s generally accepted privacy principles (GAPP)?
HIPAA Security Rule Requirements
The BI360 system and applicable controls are compliant with the applicable HIPAA Security Rule requirements set forth in the U.S. Department of Health and Human Services (HHS) Health Information Portability and Accountability Act.
What is the difference between SOC2 Type I and SOC 2 Type II?
SOC 2 reports come in two types: Type I and Type II.
- SOC 2 Type I describes the systems of the audited company and whether their design is appropriate for the relevant trust principles.
- SOC 2 Type II, on top of describing the systems, assesses their operational effectiveness.
SOC 2 Type II at Userpilot
Userpilot’s SOC 2 audit was conducted by Barr Advisory, a trusted cloud-based security and compliance advisory body. Barr is a trusted advisor to some of the fastest-growing cloud-based organizations around the globe and simplifies compliance across multiple regulatory and customer requirements in highly regulated industries including technology, financial services, healthcare, and government.
The SOC 2 examination was conducted in accordance with attestation standards established by the American Institute of Certified Public Accountants.
Userpilot’s SOC 2 Type II examination was conducted between January 1, 2021 and March 31, 2021.
The audit concluded complete compliance with the SOC 2 principles of trust.
Benefits of using SOC 2 Type II certified service providers
Now, you may wonder – “Ok, so Userpilot got SOC 2 Type II certified. But what’s in it for me?”. There are several reasons why using SOC2 Type II certified providers is a good idea for your business:
SOC 2 helps you avoid inadvertent data breaches by third parties
In 2021, data is the new black gold. As your most precious resource, you do everything to protect it from hackers, spammers, and other cyber-criminals. But what if your third-party service providers don’t? Using only SOC-2 Type II providers means you can sleep well at night and don’t worry about any data leaks or breaches through the third-party services you are using!
You avoid lawsuits
Needless to say – having your users’ data leaked through a third-party service provider’s loophole, and getting sued as a result, is every SaaS business owner’s greatest nightmare. A class-action lawsuit can mean financial ruin and bankruptcy for your business. To protect yourself from this, you need to have not only the highest security standards in your company but also use only SOC 2 Type II certified third-party service providers.
You uphold brand reputation
A lawsuit against your company can damage not only your finances but also your brand reputation – which is much harder to recover. This is another reason to go with only those service providers that take data protection extremely seriously.
You gain a competitive edge & higher trust with your customers
A lot of customers, especially established enterprise customers, require the highest data security measures from their potential suppliers. Ensuring your most valuable customers that you use only SOC 2 Type II certified service providers can help you gain trust, an advantage over other companies, and win more enterprise deals!
What does Userpilot’s SOC 2 certification mean for you in practice?
Userpilot, as a product growth platform that analyzes your users’ in-app behavior, allow you to segment your users and build personalized onboarding experiences for them, as well as to collect their sentiment and opinions via NPS and microsurveys – collects a lot of user data. It is extremely important for us to make you feel confident that your user data is in good hands – and not taken lightly. This is why we decided to subject ourselves to the SOC2 audit and certification process.
Thanks to this, you can now be confident that Userpilot:
- has access control via end-to-end encryption and two-factor authentication. You can learn more about the technologies used to ensure data security in a report issued by a reputable, independent auditor.
- uses network and application firewalls
- has intrusion-detection mechanisms in place
- uses performance monitoring tools
- uses disaster recovery tools
- has security incident handling procedures in place
- uses quality assurance and process monitoring procedures
Current and prospective customers interested in a copy of our SOC 2 Type II report may contact [email protected] to obtain more details.